- Male
- 01/01/1987
- Followed by 0 people
Recent Updates
- 𝐇𝐨𝐰 𝐀𝐫𝐞 𝐀𝐮𝐭𝐨𝐧𝐨𝐦𝐨𝐮𝐬 𝐀𝐈 𝐒𝐲𝐬𝐭𝐞𝐦𝐬 𝐓𝐫𝐚𝐧𝐬𝐟𝐨𝐫𝐦𝐢𝐧𝐠 𝐂𝐲𝐛𝐞𝐫𝐬𝐞𝐜𝐮𝐫𝐢𝐭𝐲?
Cybersecurity is entering a new era - one shaped by autonomous artificial intelligence. As threat actors become faster, more sophisticated, and increasingly automated, traditional security operations are struggling to keep pace.
Read More - https://tinyurl.com/mr43rvk5𝐇𝐨𝐰 𝐀𝐫𝐞 𝐀𝐮𝐭𝐨𝐧𝐨𝐦𝐨𝐮𝐬 𝐀𝐈 𝐒𝐲𝐬𝐭𝐞𝐦𝐬 𝐓𝐫𝐚𝐧𝐬𝐟𝐨𝐫𝐦𝐢𝐧𝐠 𝐂𝐲𝐛𝐞𝐫𝐬𝐞𝐜𝐮𝐫𝐢𝐭𝐲? Cybersecurity is entering a new era - one shaped by autonomous artificial intelligence. As threat actors become faster, more sophisticated, and increasingly automated, traditional security operations are struggling to keep pace. Read More - https://tinyurl.com/mr43rvk50 Comments 0 Shares - 𝐇𝐨𝐰 𝐭𝐨 𝐒𝐞𝐜𝐮𝐫𝐞 𝐭𝐡𝐞 𝐀𝐠𝐞𝐧𝐭𝐢𝐜 𝐄𝐧𝐭𝐞𝐫𝐩𝐫𝐢𝐬𝐞 𝐄𝐟𝐟𝐞𝐜𝐭𝐢𝐯𝐞𝐥𝐲
The rise of the agentic enterprise marks a major shift in how organizations operate, automate decisions, and execute workflows. Unlike traditional automation systems, agentic enterprises rely on AI agents that can reason, decide, and act with little human intervention.
Read More - https://tinyurl.com/9b6c4hby𝐇𝐨𝐰 𝐭𝐨 𝐒𝐞𝐜𝐮𝐫𝐞 𝐭𝐡𝐞 𝐀𝐠𝐞𝐧𝐭𝐢𝐜 𝐄𝐧𝐭𝐞𝐫𝐩𝐫𝐢𝐬𝐞 𝐄𝐟𝐟𝐞𝐜𝐭𝐢𝐯𝐞𝐥𝐲 The rise of the agentic enterprise marks a major shift in how organizations operate, automate decisions, and execute workflows. Unlike traditional automation systems, agentic enterprises rely on AI agents that can reason, decide, and act with little human intervention. Read More - https://tinyurl.com/9b6c4hby0 Comments 0 Shares - 𝐓𝐡𝐞 𝐒𝐡𝐢𝐟𝐭 𝐓𝐨𝐰𝐚𝐫𝐝 𝐐𝐮𝐚𝐧𝐭𝐮𝐦-𝐒𝐚𝐟𝐞 𝐂𝐲𝐛𝐞𝐫𝐬𝐞𝐜𝐮𝐫𝐢𝐭𝐲
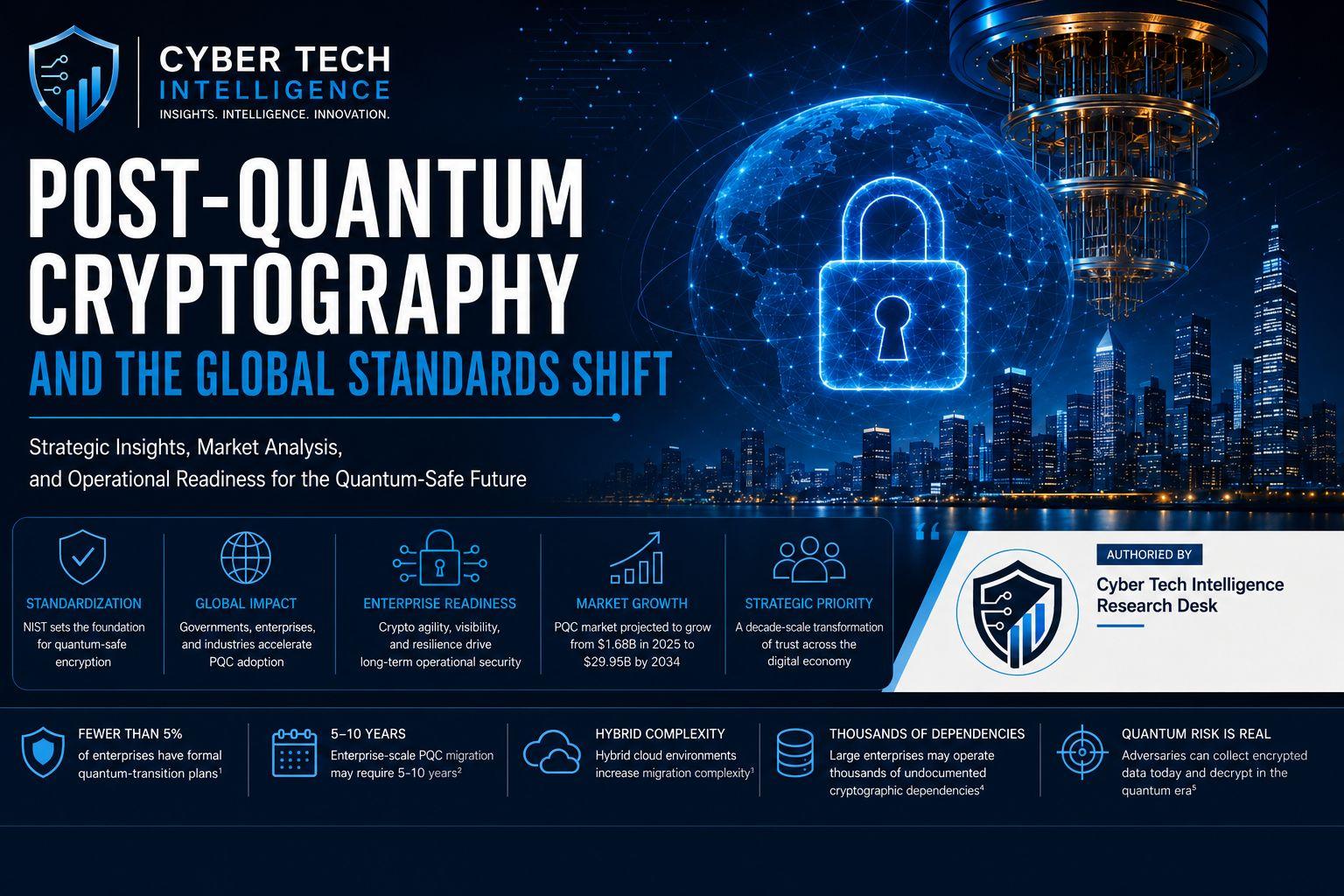
The cybersecurity world is entering one of its most significant transitions in decades. As quantum computing advances from experimental theory to practical capability, governments, regulators, and standards bodies worldwide are accelerating efforts to redefine encryption security.
Read More - https://tinyurl.com/2977d4m3𝐓𝐡𝐞 𝐒𝐡𝐢𝐟𝐭 𝐓𝐨𝐰𝐚𝐫𝐝 𝐐𝐮𝐚𝐧𝐭𝐮𝐦-𝐒𝐚𝐟𝐞 𝐂𝐲𝐛𝐞𝐫𝐬𝐞𝐜𝐮𝐫𝐢𝐭𝐲 The cybersecurity world is entering one of its most significant transitions in decades. As quantum computing advances from experimental theory to practical capability, governments, regulators, and standards bodies worldwide are accelerating efforts to redefine encryption security. Read More - https://tinyurl.com/2977d4m30 Comments 0 Shares - 𝐐𝐮𝐚𝐧𝐭𝐮𝐦 𝐑𝐞𝐚𝐝𝐢𝐧𝐞𝐬𝐬 𝐁𝐞𝐜𝐨𝐦𝐞𝐬 𝐚 𝐂𝐲𝐛𝐞𝐫𝐬𝐞𝐜𝐮𝐫𝐢𝐭𝐲 𝐏𝐫𝐢𝐨𝐫𝐢𝐭𝐲
Quantum computing is no longer a theoretical cybersecurity concern reserved for research labs. It is steadily becoming a strategic risk that enterprises, governments, and cybersecurity leaders must prepare for now.
Read More - https://tinyurl.com/2a6wa4v3𝐐𝐮𝐚𝐧𝐭𝐮𝐦 𝐑𝐞𝐚𝐝𝐢𝐧𝐞𝐬𝐬 𝐁𝐞𝐜𝐨𝐦𝐞𝐬 𝐚 𝐂𝐲𝐛𝐞𝐫𝐬𝐞𝐜𝐮𝐫𝐢𝐭𝐲 𝐏𝐫𝐢𝐨𝐫𝐢𝐭𝐲 Quantum computing is no longer a theoretical cybersecurity concern reserved for research labs. It is steadily becoming a strategic risk that enterprises, governments, and cybersecurity leaders must prepare for now. Read More - https://tinyurl.com/2a6wa4v30 Comments 0 Shares - 𝐒𝐭𝐞𝐩𝐬 𝐭𝐨 𝐄𝐧𝐡𝐚𝐧𝐜𝐞 𝐓𝐫𝐮𝐬𝐭 𝐢𝐧 𝐃𝐢𝐠𝐢𝐭𝐚𝐥 𝐁𝟐𝐁 𝐄𝐯𝐞𝐧𝐭𝐬
Digital B2B events have transformed the way organizations connect with prospects, customers, and industry leaders. From virtual conferences and webinars to hybrid networking experiences, businesses are increasingly relying on digital events to engage audiences, showcase expertise, and generate qualified leads.
Know More - https://tinyurl.com/2s333btw𝐒𝐭𝐞𝐩𝐬 𝐭𝐨 𝐄𝐧𝐡𝐚𝐧𝐜𝐞 𝐓𝐫𝐮𝐬𝐭 𝐢𝐧 𝐃𝐢𝐠𝐢𝐭𝐚𝐥 𝐁𝟐𝐁 𝐄𝐯𝐞𝐧𝐭𝐬 Digital B2B events have transformed the way organizations connect with prospects, customers, and industry leaders. From virtual conferences and webinars to hybrid networking experiences, businesses are increasingly relying on digital events to engage audiences, showcase expertise, and generate qualified leads. Know More - https://tinyurl.com/2s333btw0 Comments 0 Shares - 𝐖𝐡𝐚𝐭 𝐀𝐫𝐞 𝐭𝐡𝐞 𝐌𝐚𝐢𝐧 𝐂𝐥𝐨𝐮𝐝 𝐀𝐏𝐈 𝐒𝐞𝐜𝐮𝐫𝐢𝐭𝐲 𝐑𝐢𝐬𝐤𝐬 𝐟𝐨𝐫 𝐁𝐮𝐬𝐢𝐧𝐞𝐬𝐬𝐞𝐬?
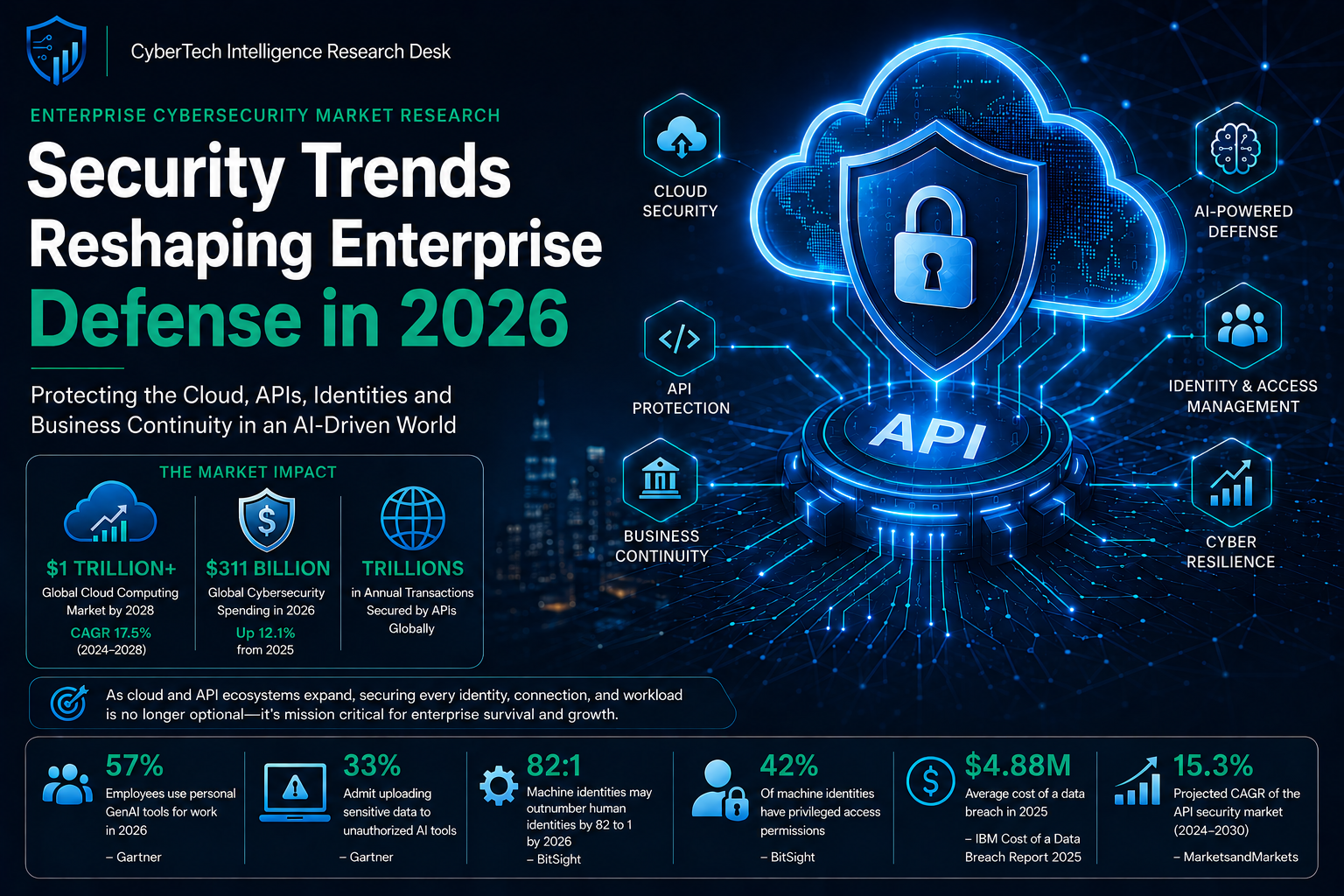
Cloud APIs have become the backbone of modern digital infrastructure. From SaaS platforms and remote collaboration tools to AI-driven applications and enterprise cloud environments, APIs enable seamless communication between systems, applications, and services.
Know More - https://tinyurl.com/y3nm6xxy𝐖𝐡𝐚𝐭 𝐀𝐫𝐞 𝐭𝐡𝐞 𝐌𝐚𝐢𝐧 𝐂𝐥𝐨𝐮𝐝 𝐀𝐏𝐈 𝐒𝐞𝐜𝐮𝐫𝐢𝐭𝐲 𝐑𝐢𝐬𝐤𝐬 𝐟𝐨𝐫 𝐁𝐮𝐬𝐢𝐧𝐞𝐬𝐬𝐞𝐬? Cloud APIs have become the backbone of modern digital infrastructure. From SaaS platforms and remote collaboration tools to AI-driven applications and enterprise cloud environments, APIs enable seamless communication between systems, applications, and services. Know More - https://tinyurl.com/y3nm6xxy0 Comments 0 Shares - 𝐇𝐨𝐰 𝐂𝐚𝐧 𝐁𝟐𝐁 𝐌𝐚𝐫𝐤𝐞𝐭𝐞𝐫𝐬 𝐑𝐚𝐧𝐤 𝐨𝐧 𝐂𝐡𝐚𝐭𝐆𝐏𝐓 𝐢𝐧 𝟐𝟎𝟐𝟔?
The way B2B buyers discover information is rapidly changing. While traditional search engines remain important, AI-powered discovery platforms are transforming how decision-makers research vendors, compare solutions, and evaluate industry expertise.
Know More - https://tinyurl.com/2s333btw𝐇𝐨𝐰 𝐂𝐚𝐧 𝐁𝟐𝐁 𝐌𝐚𝐫𝐤𝐞𝐭𝐞𝐫𝐬 𝐑𝐚𝐧𝐤 𝐨𝐧 𝐂𝐡𝐚𝐭𝐆𝐏𝐓 𝐢𝐧 𝟐𝟎𝟐𝟔? The way B2B buyers discover information is rapidly changing. While traditional search engines remain important, AI-powered discovery platforms are transforming how decision-makers research vendors, compare solutions, and evaluate industry expertise. Know More - https://tinyurl.com/2s333btw0 Comments 0 Shares - 𝐖𝐡𝐚𝐭 𝐀𝐫𝐞 𝐭𝐡𝐞 𝐓𝐨𝐩 𝐁𝟐𝐁 𝐀𝐈 𝐓𝐞𝐜𝐡 𝐂𝐨𝐦𝐩𝐚𝐧𝐢𝐞𝐬 𝐢𝐧 𝟐𝟎𝟐𝟔?
Artificial intelligence has rapidly evolved from an emerging technology into a critical business driver across industries. In 2026, B2B organizations are increasingly relying on AI-powered platforms to improve productivity, automate workflows, strengthen cybersecurity, personalize customer engagement, and make more informed decisions.
Know More - https://tinyurl.com/2s333btw𝐖𝐡𝐚𝐭 𝐀𝐫𝐞 𝐭𝐡𝐞 𝐓𝐨𝐩 𝐁𝟐𝐁 𝐀𝐈 𝐓𝐞𝐜𝐡 𝐂𝐨𝐦𝐩𝐚𝐧𝐢𝐞𝐬 𝐢𝐧 𝟐𝟎𝟐𝟔? Artificial intelligence has rapidly evolved from an emerging technology into a critical business driver across industries. In 2026, B2B organizations are increasingly relying on AI-powered platforms to improve productivity, automate workflows, strengthen cybersecurity, personalize customer engagement, and make more informed decisions. Know More - https://tinyurl.com/2s333btw0 Comments 0 Shares - 𝟏𝟎 𝐁𝐞𝐬𝐭 𝐖𝐞𝐛𝐢𝐧𝐚𝐫 𝐋𝐚𝐧𝐝𝐢𝐧𝐠 𝐏𝐚𝐠𝐞 𝐄𝐱𝐚𝐦𝐩𝐥𝐞𝐬 𝐭𝐨 𝐈𝐧𝐬𝐩𝐢𝐫𝐞 𝐘𝐨𝐮
Webinars have become one of the most effective tools for B2B lead generation, audience engagement, and brand positioning. However, even the most valuable webinar content may struggle to attract registrations without a high-performing landing page.
Know More - https://intentamplify.com/mediakit/𝟏𝟎 𝐁𝐞𝐬𝐭 𝐖𝐞𝐛𝐢𝐧𝐚𝐫 𝐋𝐚𝐧𝐝𝐢𝐧𝐠 𝐏𝐚𝐠𝐞 𝐄𝐱𝐚𝐦𝐩𝐥𝐞𝐬 𝐭𝐨 𝐈𝐧𝐬𝐩𝐢𝐫𝐞 𝐘𝐨𝐮 Webinars have become one of the most effective tools for B2B lead generation, audience engagement, and brand positioning. However, even the most valuable webinar content may struggle to attract registrations without a high-performing landing page. Know More - https://intentamplify.com/mediakit/0 Comments 0 Shares - 𝐀𝐏𝐈 𝐚𝐧𝐝 𝐂𝐥𝐨𝐮𝐝 𝐓𝐡𝐫𝐞𝐚𝐭 𝐌𝐨𝐧𝐢𝐭𝐨𝐫
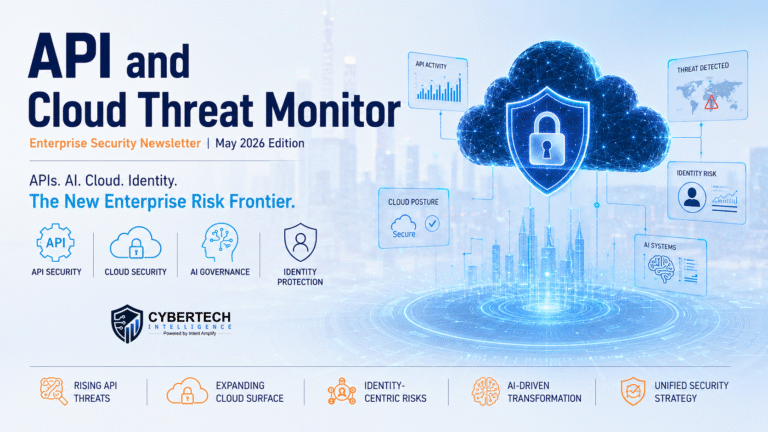
As enterprises accelerate cloud adoption and API-driven innovation, cybersecurity teams face an increasingly difficult challenge: maintaining visibility across dynamic, interconnected environments. APIs and cloud services have become foundational to digital business operations, but they have also expanded the threat landscape in ways traditional security models struggle to address.
Know More - https://cybertechnologyinsights.com/download-media-kit/𝐀𝐏𝐈 𝐚𝐧𝐝 𝐂𝐥𝐨𝐮𝐝 𝐓𝐡𝐫𝐞𝐚𝐭 𝐌𝐨𝐧𝐢𝐭𝐨𝐫 As enterprises accelerate cloud adoption and API-driven innovation, cybersecurity teams face an increasingly difficult challenge: maintaining visibility across dynamic, interconnected environments. APIs and cloud services have become foundational to digital business operations, but they have also expanded the threat landscape in ways traditional security models struggle to address. Know More - https://cybertechnologyinsights.com/download-media-kit/0 Comments 0 Shares
More Stories