SPARK Matrix™: AI Observability Solutions
As enterprises accelerate the deployment of artificial intelligence (AI) and machine learning (ML) models across business-critical functions, ensuring transparency, reliability, and governance has become a top priority. QKS Group’s AI Observability Solutions market research delivers an in-depth analysis of the global market, highlighting emerging technology innovations, evolving market trends, and the future outlook shaping AI observability adoption worldwide.
Click here for more information : https://qksgroup.com/market-research/spark-matrix-ai-observability-solutions-q3-2025-9029
Understanding the AI Observability Solutions Market
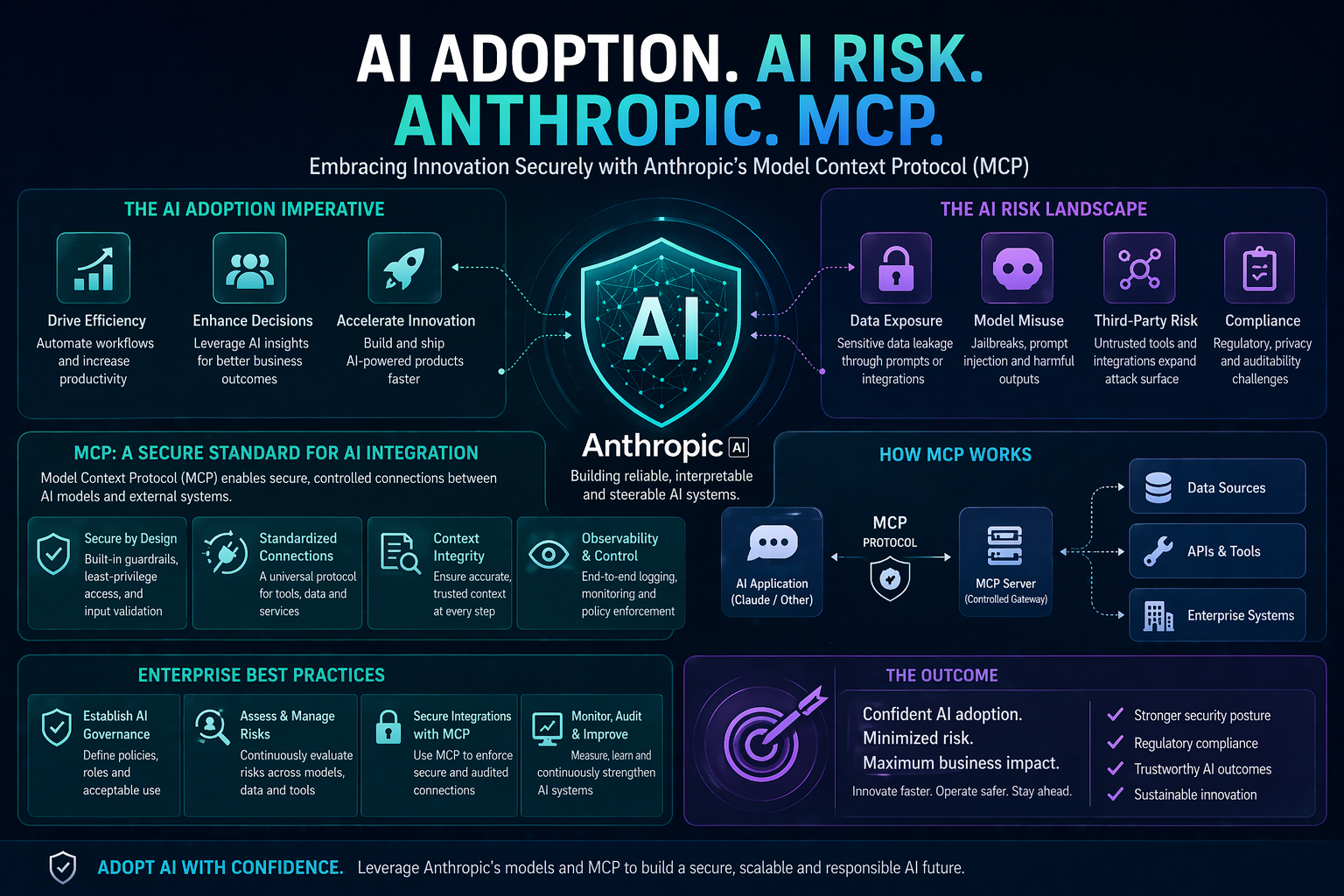
AI Observability Solutions are purpose-built software platforms that enable organizations to monitor, analyze, and manage AI and ML systems throughout their lifecycle, from model development to production deployment. According to Prabhat Mishra, Analyst at QKS Group, these solutions empower enterprises with capabilities such as real-time model performance monitoring, drift detection, anomaly identification, bias and fairness assessment, explainability, and lineage tracking. Collectively, these functionalities help organizations maintain trustworthy, compliant, and high-performing AI systems at scale.
With AI models becoming increasingly complex and embedded in decision-making processes, traditional monitoring approaches are no longer sufficient. AI observability bridges this gap by providing actionable insights to data science, engineering, compliance, and business teams, ensuring operational resilience while supporting responsible AI initiatives.
Key Market Drivers and Technology Trends
The AI Observability market is witnessing robust growth driven by several factors:
• Rapid enterprise AI adoption across industries such as BFSI, healthcare, retail, manufacturing, and telecom
• Growing regulatory scrutiny around AI ethics, fairness, transparency, and accountability
• Rising operational risks associated with model drift, data quality issues, and bias in production AI systems
• Demand for explainable and auditable AI to support governance and compliance requirements
Emerging trends such as automated root-cause analysis, continuous model validation, AI risk scoring, and tighter integration with MLOps and data observability platforms are reshaping how organizations manage AI at scale.
Strategic Value for Vendors and Enterprises
QKS Group’s AI Observability Solutions market research provides strategic insights for technology vendors, enabling them to refine product strategies, identify white-space opportunities, and align innovation roadmaps with enterprise requirements. For buyers and end users, the research offers a structured framework to evaluate vendor capabilities, understand competitive differentiation, and assess market positioning against evolving governance and operational needs.
Click here to Download Sample Report : https://qksgroup.com/download-sample-form/%20?id=9029
Competitive Landscape and SPARK Matrix™ Analysis
A key highlight of the research is the proprietary SPARK Matrix™ analysis, which delivers a comprehensive competitive assessment of leading AI Observability vendors with global impact. The SPARK Matrix ranks vendors based on technology excellence and customer impact, providing clear visibility into market leaders, challengers, and emerging players.
Vendors evaluated in the study include Acceldata, Aisera, CalypsoAI, Cisco (Splunk), Databricks, Datadog, Dataiku, Dynatrace, Elastic, Evidently AI, Fiddler AI, Grafana Labs, Honeycomb.io, Kyndryl, New Relic, Snowflake, and WhyLabs. This detailed evaluation enables enterprises to make informed purchasing decisions while helping vendors benchmark their offerings against competitors.
Future Outlook: Scaling Responsible and Observable AI
As AI systems continue to influence high-stakes business outcomes, AI Observability Solutions will become foundational to enterprise AI strategies. Organizations that invest in observability will be better positioned to minimize risk exposure, ensure regulatory compliance, and sustain long-term AI performance. By delivering visibility, accountability, and governance across complex AI environments, AI observability platforms are set to play a critical role in the future of responsible AI adoption.
QKS Group’s AI Observability Solutions market research serves as a trusted resource for enterprises and technology providers seeking clarity, strategic direction, and competitive intelligence in this rapidly evolving market.
As enterprises accelerate the deployment of artificial intelligence (AI) and machine learning (ML) models across business-critical functions, ensuring transparency, reliability, and governance has become a top priority. QKS Group’s AI Observability Solutions market research delivers an in-depth analysis of the global market, highlighting emerging technology innovations, evolving market trends, and the future outlook shaping AI observability adoption worldwide.
Click here for more information : https://qksgroup.com/market-research/spark-matrix-ai-observability-solutions-q3-2025-9029
Understanding the AI Observability Solutions Market
AI Observability Solutions are purpose-built software platforms that enable organizations to monitor, analyze, and manage AI and ML systems throughout their lifecycle, from model development to production deployment. According to Prabhat Mishra, Analyst at QKS Group, these solutions empower enterprises with capabilities such as real-time model performance monitoring, drift detection, anomaly identification, bias and fairness assessment, explainability, and lineage tracking. Collectively, these functionalities help organizations maintain trustworthy, compliant, and high-performing AI systems at scale.
With AI models becoming increasingly complex and embedded in decision-making processes, traditional monitoring approaches are no longer sufficient. AI observability bridges this gap by providing actionable insights to data science, engineering, compliance, and business teams, ensuring operational resilience while supporting responsible AI initiatives.
Key Market Drivers and Technology Trends
The AI Observability market is witnessing robust growth driven by several factors:
• Rapid enterprise AI adoption across industries such as BFSI, healthcare, retail, manufacturing, and telecom
• Growing regulatory scrutiny around AI ethics, fairness, transparency, and accountability
• Rising operational risks associated with model drift, data quality issues, and bias in production AI systems
• Demand for explainable and auditable AI to support governance and compliance requirements
Emerging trends such as automated root-cause analysis, continuous model validation, AI risk scoring, and tighter integration with MLOps and data observability platforms are reshaping how organizations manage AI at scale.
Strategic Value for Vendors and Enterprises
QKS Group’s AI Observability Solutions market research provides strategic insights for technology vendors, enabling them to refine product strategies, identify white-space opportunities, and align innovation roadmaps with enterprise requirements. For buyers and end users, the research offers a structured framework to evaluate vendor capabilities, understand competitive differentiation, and assess market positioning against evolving governance and operational needs.
Click here to Download Sample Report : https://qksgroup.com/download-sample-form/%20?id=9029
Competitive Landscape and SPARK Matrix™ Analysis
A key highlight of the research is the proprietary SPARK Matrix™ analysis, which delivers a comprehensive competitive assessment of leading AI Observability vendors with global impact. The SPARK Matrix ranks vendors based on technology excellence and customer impact, providing clear visibility into market leaders, challengers, and emerging players.
Vendors evaluated in the study include Acceldata, Aisera, CalypsoAI, Cisco (Splunk), Databricks, Datadog, Dataiku, Dynatrace, Elastic, Evidently AI, Fiddler AI, Grafana Labs, Honeycomb.io, Kyndryl, New Relic, Snowflake, and WhyLabs. This detailed evaluation enables enterprises to make informed purchasing decisions while helping vendors benchmark their offerings against competitors.
Future Outlook: Scaling Responsible and Observable AI
As AI systems continue to influence high-stakes business outcomes, AI Observability Solutions will become foundational to enterprise AI strategies. Organizations that invest in observability will be better positioned to minimize risk exposure, ensure regulatory compliance, and sustain long-term AI performance. By delivering visibility, accountability, and governance across complex AI environments, AI observability platforms are set to play a critical role in the future of responsible AI adoption.
QKS Group’s AI Observability Solutions market research serves as a trusted resource for enterprises and technology providers seeking clarity, strategic direction, and competitive intelligence in this rapidly evolving market.
SPARK Matrix™: AI Observability Solutions
As enterprises accelerate the deployment of artificial intelligence (AI) and machine learning (ML) models across business-critical functions, ensuring transparency, reliability, and governance has become a top priority. QKS Group’s AI Observability Solutions market research delivers an in-depth analysis of the global market, highlighting emerging technology innovations, evolving market trends, and the future outlook shaping AI observability adoption worldwide.
Click here for more information : https://qksgroup.com/market-research/spark-matrix-ai-observability-solutions-q3-2025-9029
Understanding the AI Observability Solutions Market
AI Observability Solutions are purpose-built software platforms that enable organizations to monitor, analyze, and manage AI and ML systems throughout their lifecycle, from model development to production deployment. According to Prabhat Mishra, Analyst at QKS Group, these solutions empower enterprises with capabilities such as real-time model performance monitoring, drift detection, anomaly identification, bias and fairness assessment, explainability, and lineage tracking. Collectively, these functionalities help organizations maintain trustworthy, compliant, and high-performing AI systems at scale.
With AI models becoming increasingly complex and embedded in decision-making processes, traditional monitoring approaches are no longer sufficient. AI observability bridges this gap by providing actionable insights to data science, engineering, compliance, and business teams, ensuring operational resilience while supporting responsible AI initiatives.
Key Market Drivers and Technology Trends
The AI Observability market is witnessing robust growth driven by several factors:
• Rapid enterprise AI adoption across industries such as BFSI, healthcare, retail, manufacturing, and telecom
• Growing regulatory scrutiny around AI ethics, fairness, transparency, and accountability
• Rising operational risks associated with model drift, data quality issues, and bias in production AI systems
• Demand for explainable and auditable AI to support governance and compliance requirements
Emerging trends such as automated root-cause analysis, continuous model validation, AI risk scoring, and tighter integration with MLOps and data observability platforms are reshaping how organizations manage AI at scale.
Strategic Value for Vendors and Enterprises
QKS Group’s AI Observability Solutions market research provides strategic insights for technology vendors, enabling them to refine product strategies, identify white-space opportunities, and align innovation roadmaps with enterprise requirements. For buyers and end users, the research offers a structured framework to evaluate vendor capabilities, understand competitive differentiation, and assess market positioning against evolving governance and operational needs.
Click here to Download Sample Report : https://qksgroup.com/download-sample-form/%20?id=9029
Competitive Landscape and SPARK Matrix™ Analysis
A key highlight of the research is the proprietary SPARK Matrix™ analysis, which delivers a comprehensive competitive assessment of leading AI Observability vendors with global impact. The SPARK Matrix ranks vendors based on technology excellence and customer impact, providing clear visibility into market leaders, challengers, and emerging players.
Vendors evaluated in the study include Acceldata, Aisera, CalypsoAI, Cisco (Splunk), Databricks, Datadog, Dataiku, Dynatrace, Elastic, Evidently AI, Fiddler AI, Grafana Labs, Honeycomb.io, Kyndryl, New Relic, Snowflake, and WhyLabs. This detailed evaluation enables enterprises to make informed purchasing decisions while helping vendors benchmark their offerings against competitors.
Future Outlook: Scaling Responsible and Observable AI
As AI systems continue to influence high-stakes business outcomes, AI Observability Solutions will become foundational to enterprise AI strategies. Organizations that invest in observability will be better positioned to minimize risk exposure, ensure regulatory compliance, and sustain long-term AI performance. By delivering visibility, accountability, and governance across complex AI environments, AI observability platforms are set to play a critical role in the future of responsible AI adoption.
QKS Group’s AI Observability Solutions market research serves as a trusted resource for enterprises and technology providers seeking clarity, strategic direction, and competitive intelligence in this rapidly evolving market.