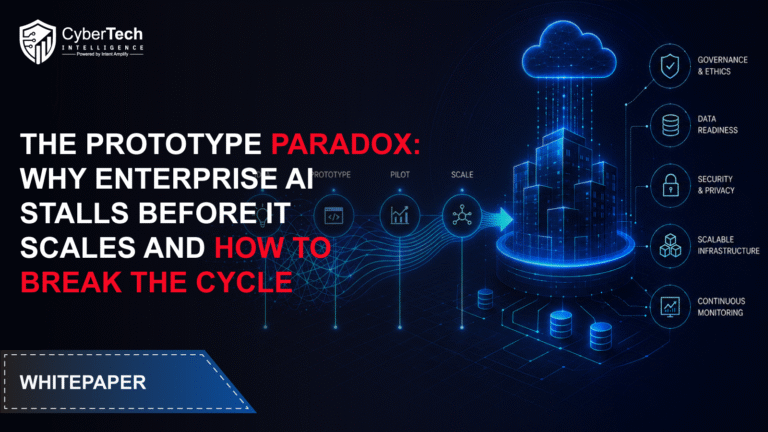
The Prototype Paradox: Why Enterprise AI Stalls Before It Scales and How to Break the Cycle
Turning AI Potential into Production Reality
Artificial intelligence has become a defining priority for enterprise leaders across the United States, with adoption accelerating across every major industry. Yet despite billions in investment and widespread experimentation, a persistent challenge remains: most AI initiatives never scale beyond the prototype stage.
The whitepaper “The Prototype Paradox: Why Enterprise AI Stalls Before It Scales and How to Break the Cycle” explores why this execution gap exists—and why it continues to widen even as AI capabilities become more advanced.
While nearly every organization is actively exploring AI, only a small fraction successfully translate pilots into production-grade systems that deliver sustained business value. This disconnect is now referred to as the Prototype Paradox—the growing gap between AI experimentation and enterprise-scale impact.
Read More: https://tinyurl.com/44mspr9n
Why AI Stalls Before Scaling
At the core of the Prototype Paradox is not a failure of technology, but a failure of execution maturity.
Enterprises often begin AI journeys with strong enthusiasm. Pilot programs are launched, proof-of-concepts demonstrate value, and internal support increases. However, when organizations attempt to move from controlled environments to real-world production systems, complexity escalates rapidly.
The whitepaper identifies key friction points:
• Fragmented and inconsistent data ecosystems
• Weak governance and oversight structures
• Legacy workflows that resist automation
• Limited workforce readiness for AI-driven operations
• Lack of clear ROI measurement frameworks
These challenges collectively create an environment where AI works well in isolation but struggles in enterprise-scale deployment.
As highlighted in industry research, a significant percentage of AI initiatives fail to move beyond proof-of-concept due to insufficient data readiness, governance gaps, or unclear business alignment.
The Hidden Cost of AI Experimentation Without Scale
One of the most important insights from the whitepaper is that pilot-heavy AI environments often generate hidden technical and financial debt.
While experimentation may appear low-risk, it frequently leads to:
• Duplicate AI tools across departments
• Fragmented infrastructure investments
• Uncontrolled model sprawl
• Inconsistent security and compliance oversight
• Rising operational complexity over time
As organizations expand experimentation without consolidation, they inadvertently slow down production readiness.
What begins as innovation momentum gradually turns into execution stagnation.
Five Structural Barriers Blocking AI Scale
The whitepaper identifies five core barriers that consistently prevent AI initiatives from reaching enterprise-scale deployment:
1. Data Fragmentation
Enterprise AI systems rely heavily on unified, high-quality data. However, most organizations operate across siloed systems built over decades. This fragmentation undermines model reliability and limits scalability.
2. Governance Gaps
Many enterprises lack mature AI governance frameworks. Without clear accountability, oversight, and compliance structures, scaling becomes risky and inconsistent.
3. Workforce Limitations
AI transformation requires specialized skills in engineering, data science, and AI operations. Talent shortages significantly slow down scaling efforts.
4. Legacy Operating Models
Traditional workflows are often incompatible with AI-native execution. Without redesigning business processes, AI remains an add-on rather than a core capability.
5. ROI Measurement Challenges
Many organizations fail to define clear business outcomes for AI systems, leading to difficulty in proving long-term value and justifying scale.
Together, these barriers explain why so many AI initiatives remain stuck in pilot mode despite strong initial results.
Why Only a Small Percentage of Companies Scale AI Successfully
A critical finding in the whitepaper is that only a small group of enterprises successfully bridge the gap between experimentation and production-scale AI.
These organizations typically:
• Consolidate AI platforms instead of fragmenting tools
• Align AI initiatives with measurable business outcomes
• Redesign workflows instead of automating outdated processes
• Invest heavily in data and infrastructure readiness
• Establish strong executive governance structures
This group consistently outperforms peers in ROI realization, operational efficiency, and long-term AI impact.
Breaking the Prototype Paradox
The whitepaper introduces a structured approach for moving from prototype to production, built around five transformation imperatives:
1. Modernize data foundations before scaling AI
2. Establish trust, governance, and security early in the lifecycle
3. Close the AI talent gap through strategic partnerships
4. Redesign workflows for AI-first execution models
5. Tie every AI initiative to measurable business outcomes
These principles shift AI deployment from experimental innovation to structured enterprise transformation.
The Role of Leadership in AI Success
A key message throughout the whitepaper is that AI scalability is not purely a technical challenge—it is a leadership challenge.
CIOs, CISOs, and enterprise executives must evaluate readiness across:
• Data infrastructure maturity
• Governance and oversight capabilities
• Workforce readiness
• Security and compliance frameworks
• Business alignment and ROI tracking
Without these foundational elements, scaling AI introduces operational and financial risk rather than value creation.
The Road Ahead for Enterprise AI
AI adoption is expected to continue accelerating across industries, with agentic and autonomous systems becoming increasingly embedded in enterprise operations.
However, the whitepaper emphasizes that future success will not be determined by who adopts AI first, but by who scales it effectively.
Enterprises that solve the Prototype Paradox will gain:
• Faster innovation cycles
• Stronger operational efficiency
• Improved decision-making capabilities
• Scalable and secure AI systems
• Sustainable competitive advantage
Those that fail to address foundational gaps risk remaining stuck in perpetual experimentation cycles.
Final Takeaway
The Prototype Paradox is redefining how enterprises think about AI success.
The challenge is no longer building models—it is building systems that can scale them responsibly, securely, and effectively across the organization.
Organizations that treat AI as an integrated transformation strategy—rather than isolated experimentation—will lead the next wave of enterprise innovation.
Read More: https://tinyurl.com/44mspr9n
Turning AI Potential into Production Reality
Artificial intelligence has become a defining priority for enterprise leaders across the United States, with adoption accelerating across every major industry. Yet despite billions in investment and widespread experimentation, a persistent challenge remains: most AI initiatives never scale beyond the prototype stage.
The whitepaper “The Prototype Paradox: Why Enterprise AI Stalls Before It Scales and How to Break the Cycle” explores why this execution gap exists—and why it continues to widen even as AI capabilities become more advanced.
While nearly every organization is actively exploring AI, only a small fraction successfully translate pilots into production-grade systems that deliver sustained business value. This disconnect is now referred to as the Prototype Paradox—the growing gap between AI experimentation and enterprise-scale impact.
Read More: https://tinyurl.com/44mspr9n
Why AI Stalls Before Scaling
At the core of the Prototype Paradox is not a failure of technology, but a failure of execution maturity.
Enterprises often begin AI journeys with strong enthusiasm. Pilot programs are launched, proof-of-concepts demonstrate value, and internal support increases. However, when organizations attempt to move from controlled environments to real-world production systems, complexity escalates rapidly.
The whitepaper identifies key friction points:
• Fragmented and inconsistent data ecosystems
• Weak governance and oversight structures
• Legacy workflows that resist automation
• Limited workforce readiness for AI-driven operations
• Lack of clear ROI measurement frameworks
These challenges collectively create an environment where AI works well in isolation but struggles in enterprise-scale deployment.
As highlighted in industry research, a significant percentage of AI initiatives fail to move beyond proof-of-concept due to insufficient data readiness, governance gaps, or unclear business alignment.
The Hidden Cost of AI Experimentation Without Scale
One of the most important insights from the whitepaper is that pilot-heavy AI environments often generate hidden technical and financial debt.
While experimentation may appear low-risk, it frequently leads to:
• Duplicate AI tools across departments
• Fragmented infrastructure investments
• Uncontrolled model sprawl
• Inconsistent security and compliance oversight
• Rising operational complexity over time
As organizations expand experimentation without consolidation, they inadvertently slow down production readiness.
What begins as innovation momentum gradually turns into execution stagnation.
Five Structural Barriers Blocking AI Scale
The whitepaper identifies five core barriers that consistently prevent AI initiatives from reaching enterprise-scale deployment:
1. Data Fragmentation
Enterprise AI systems rely heavily on unified, high-quality data. However, most organizations operate across siloed systems built over decades. This fragmentation undermines model reliability and limits scalability.
2. Governance Gaps
Many enterprises lack mature AI governance frameworks. Without clear accountability, oversight, and compliance structures, scaling becomes risky and inconsistent.
3. Workforce Limitations
AI transformation requires specialized skills in engineering, data science, and AI operations. Talent shortages significantly slow down scaling efforts.
4. Legacy Operating Models
Traditional workflows are often incompatible with AI-native execution. Without redesigning business processes, AI remains an add-on rather than a core capability.
5. ROI Measurement Challenges
Many organizations fail to define clear business outcomes for AI systems, leading to difficulty in proving long-term value and justifying scale.
Together, these barriers explain why so many AI initiatives remain stuck in pilot mode despite strong initial results.
Why Only a Small Percentage of Companies Scale AI Successfully
A critical finding in the whitepaper is that only a small group of enterprises successfully bridge the gap between experimentation and production-scale AI.
These organizations typically:
• Consolidate AI platforms instead of fragmenting tools
• Align AI initiatives with measurable business outcomes
• Redesign workflows instead of automating outdated processes
• Invest heavily in data and infrastructure readiness
• Establish strong executive governance structures
This group consistently outperforms peers in ROI realization, operational efficiency, and long-term AI impact.
Breaking the Prototype Paradox
The whitepaper introduces a structured approach for moving from prototype to production, built around five transformation imperatives:
1. Modernize data foundations before scaling AI
2. Establish trust, governance, and security early in the lifecycle
3. Close the AI talent gap through strategic partnerships
4. Redesign workflows for AI-first execution models
5. Tie every AI initiative to measurable business outcomes
These principles shift AI deployment from experimental innovation to structured enterprise transformation.
The Role of Leadership in AI Success
A key message throughout the whitepaper is that AI scalability is not purely a technical challenge—it is a leadership challenge.
CIOs, CISOs, and enterprise executives must evaluate readiness across:
• Data infrastructure maturity
• Governance and oversight capabilities
• Workforce readiness
• Security and compliance frameworks
• Business alignment and ROI tracking
Without these foundational elements, scaling AI introduces operational and financial risk rather than value creation.
The Road Ahead for Enterprise AI
AI adoption is expected to continue accelerating across industries, with agentic and autonomous systems becoming increasingly embedded in enterprise operations.
However, the whitepaper emphasizes that future success will not be determined by who adopts AI first, but by who scales it effectively.
Enterprises that solve the Prototype Paradox will gain:
• Faster innovation cycles
• Stronger operational efficiency
• Improved decision-making capabilities
• Scalable and secure AI systems
• Sustainable competitive advantage
Those that fail to address foundational gaps risk remaining stuck in perpetual experimentation cycles.
Final Takeaway
The Prototype Paradox is redefining how enterprises think about AI success.
The challenge is no longer building models—it is building systems that can scale them responsibly, securely, and effectively across the organization.
Organizations that treat AI as an integrated transformation strategy—rather than isolated experimentation—will lead the next wave of enterprise innovation.
Read More: https://tinyurl.com/44mspr9n
The Prototype Paradox: Why Enterprise AI Stalls Before It Scales and How to Break the Cycle
Turning AI Potential into Production Reality
Artificial intelligence has become a defining priority for enterprise leaders across the United States, with adoption accelerating across every major industry. Yet despite billions in investment and widespread experimentation, a persistent challenge remains: most AI initiatives never scale beyond the prototype stage.
The whitepaper “The Prototype Paradox: Why Enterprise AI Stalls Before It Scales and How to Break the Cycle” explores why this execution gap exists—and why it continues to widen even as AI capabilities become more advanced.
While nearly every organization is actively exploring AI, only a small fraction successfully translate pilots into production-grade systems that deliver sustained business value. This disconnect is now referred to as the Prototype Paradox—the growing gap between AI experimentation and enterprise-scale impact.
Read More: https://tinyurl.com/44mspr9n
Why AI Stalls Before Scaling
At the core of the Prototype Paradox is not a failure of technology, but a failure of execution maturity.
Enterprises often begin AI journeys with strong enthusiasm. Pilot programs are launched, proof-of-concepts demonstrate value, and internal support increases. However, when organizations attempt to move from controlled environments to real-world production systems, complexity escalates rapidly.
The whitepaper identifies key friction points:
• Fragmented and inconsistent data ecosystems
• Weak governance and oversight structures
• Legacy workflows that resist automation
• Limited workforce readiness for AI-driven operations
• Lack of clear ROI measurement frameworks
These challenges collectively create an environment where AI works well in isolation but struggles in enterprise-scale deployment.
As highlighted in industry research, a significant percentage of AI initiatives fail to move beyond proof-of-concept due to insufficient data readiness, governance gaps, or unclear business alignment.
The Hidden Cost of AI Experimentation Without Scale
One of the most important insights from the whitepaper is that pilot-heavy AI environments often generate hidden technical and financial debt.
While experimentation may appear low-risk, it frequently leads to:
• Duplicate AI tools across departments
• Fragmented infrastructure investments
• Uncontrolled model sprawl
• Inconsistent security and compliance oversight
• Rising operational complexity over time
As organizations expand experimentation without consolidation, they inadvertently slow down production readiness.
What begins as innovation momentum gradually turns into execution stagnation.
Five Structural Barriers Blocking AI Scale
The whitepaper identifies five core barriers that consistently prevent AI initiatives from reaching enterprise-scale deployment:
1. Data Fragmentation
Enterprise AI systems rely heavily on unified, high-quality data. However, most organizations operate across siloed systems built over decades. This fragmentation undermines model reliability and limits scalability.
2. Governance Gaps
Many enterprises lack mature AI governance frameworks. Without clear accountability, oversight, and compliance structures, scaling becomes risky and inconsistent.
3. Workforce Limitations
AI transformation requires specialized skills in engineering, data science, and AI operations. Talent shortages significantly slow down scaling efforts.
4. Legacy Operating Models
Traditional workflows are often incompatible with AI-native execution. Without redesigning business processes, AI remains an add-on rather than a core capability.
5. ROI Measurement Challenges
Many organizations fail to define clear business outcomes for AI systems, leading to difficulty in proving long-term value and justifying scale.
Together, these barriers explain why so many AI initiatives remain stuck in pilot mode despite strong initial results.
Why Only a Small Percentage of Companies Scale AI Successfully
A critical finding in the whitepaper is that only a small group of enterprises successfully bridge the gap between experimentation and production-scale AI.
These organizations typically:
• Consolidate AI platforms instead of fragmenting tools
• Align AI initiatives with measurable business outcomes
• Redesign workflows instead of automating outdated processes
• Invest heavily in data and infrastructure readiness
• Establish strong executive governance structures
This group consistently outperforms peers in ROI realization, operational efficiency, and long-term AI impact.
Breaking the Prototype Paradox
The whitepaper introduces a structured approach for moving from prototype to production, built around five transformation imperatives:
1. Modernize data foundations before scaling AI
2. Establish trust, governance, and security early in the lifecycle
3. Close the AI talent gap through strategic partnerships
4. Redesign workflows for AI-first execution models
5. Tie every AI initiative to measurable business outcomes
These principles shift AI deployment from experimental innovation to structured enterprise transformation.
The Role of Leadership in AI Success
A key message throughout the whitepaper is that AI scalability is not purely a technical challenge—it is a leadership challenge.
CIOs, CISOs, and enterprise executives must evaluate readiness across:
• Data infrastructure maturity
• Governance and oversight capabilities
• Workforce readiness
• Security and compliance frameworks
• Business alignment and ROI tracking
Without these foundational elements, scaling AI introduces operational and financial risk rather than value creation.
The Road Ahead for Enterprise AI
AI adoption is expected to continue accelerating across industries, with agentic and autonomous systems becoming increasingly embedded in enterprise operations.
However, the whitepaper emphasizes that future success will not be determined by who adopts AI first, but by who scales it effectively.
Enterprises that solve the Prototype Paradox will gain:
• Faster innovation cycles
• Stronger operational efficiency
• Improved decision-making capabilities
• Scalable and secure AI systems
• Sustainable competitive advantage
Those that fail to address foundational gaps risk remaining stuck in perpetual experimentation cycles.
Final Takeaway
The Prototype Paradox is redefining how enterprises think about AI success.
The challenge is no longer building models—it is building systems that can scale them responsibly, securely, and effectively across the organization.
Organizations that treat AI as an integrated transformation strategy—rather than isolated experimentation—will lead the next wave of enterprise innovation.
Read More: https://tinyurl.com/44mspr9n
0 Comments
0 Shares