Privacy Meets Precision: The Rise of Ethical Intent Data in B2B Marketing
B2B marketing is entering a new era one where privacy, transparency, and trust matter just as much as targeting and personalization. For years, marketers relied heavily on third-party tracking and aggressive data collection to understand buyer behavior. But today, that approach is rapidly losing effectiveness.
As privacy regulations tighten and buyers become more aware of how their data is used, businesses are turning to a more responsible approach: ethical intent data.
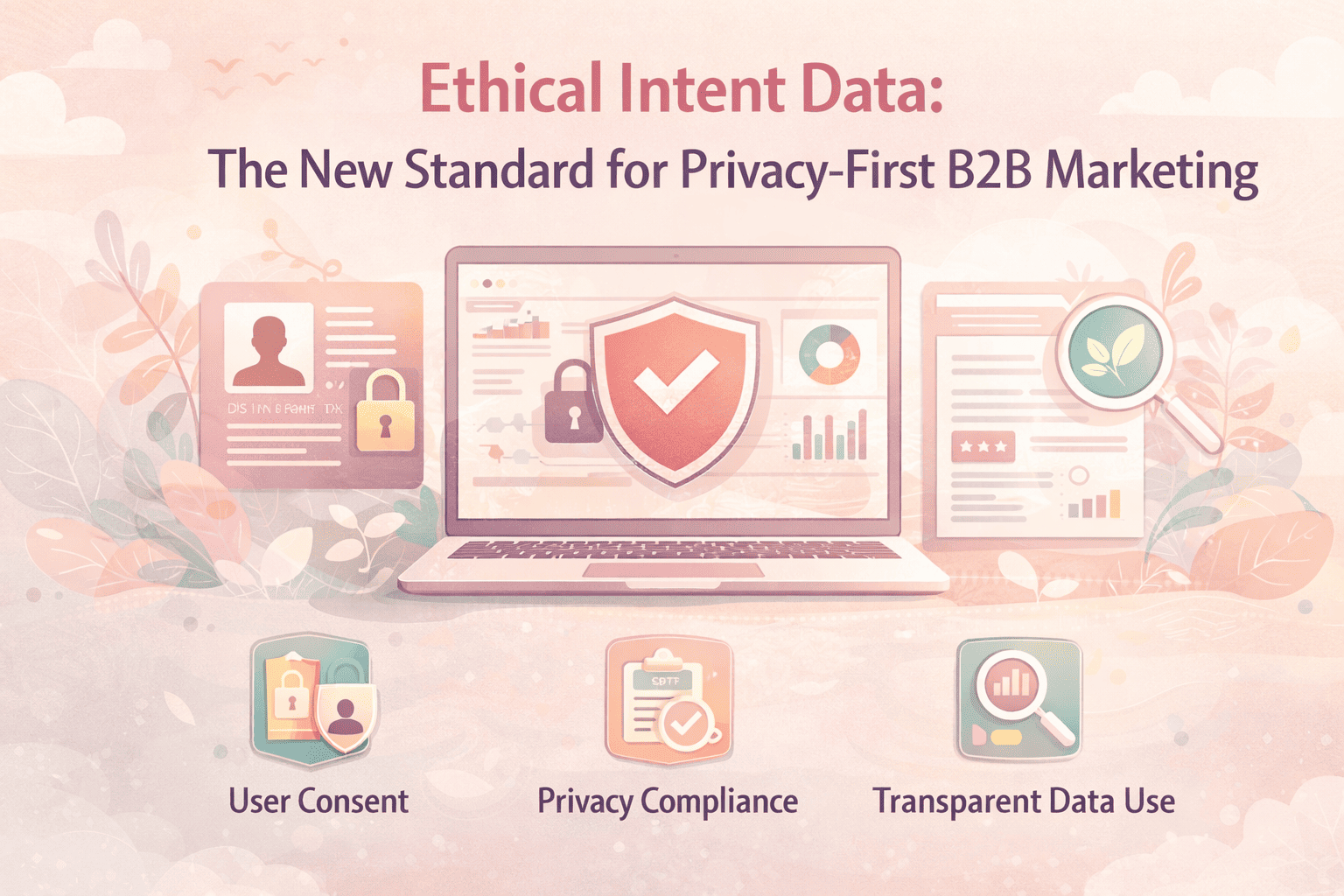
What Is Ethical Intent Data?
Ethical intent data refers to buyer behavior insights collected transparently, responsibly, and with user consent. It helps marketers understand what prospects are researching and when they may be ready to buy without violating privacy expectations.
Unlike traditional intent data practices, ethical intent data focuses on:
• Consent-based data collection
• Transparency in how data is used
• Compliance with privacy regulations
• Respect for user trust and control
In simple terms, it’s about gathering valuable insights while putting privacy and ethics first.
Why Traditional Intent Data Is Losing Relevance
Traditional intent data models often relied on third-party cookies and unclear tracking methods. But several major changes are reshaping the landscape:
• Browsers are phasing out third-party cookies
• Privacy laws are becoming stricter worldwide
• Buyers are demanding greater transparency
• Companies face increasing compliance risks
As a result, many older tracking methods are becoming less reliable and more difficult to justify.
Why Top B2B Brands Are Switching to Ethical Intent Data
1. Building Trust with Buyers
Trust is now a competitive advantage. Brands that respect privacy and communicate transparently are more likely to earn long-term customer loyalty.
2. Staying Compliant with Privacy Regulations
Ethical intent data helps companies align with evolving privacy laws and avoid legal or reputational risks.
3. Improving Data Accuracy
Consent-driven and first-party data sources are often more reliable because they come directly from engaged users.
4. Preparing for a Cookie-Free Future
As third-party cookies disappear, ethical data strategies offer a sustainable and future-ready alternative.
5. Delivering Smarter Personalization
Ethical intent data still allows for relevant targeting and personalization without intrusive tracking methods.
How Ethical Intent Data Works
Ethical intent data typically combines:
• First-party data: Website visits, CRM insights, email engagement
• Contextual signals: Content topics and research behavior
• Permission-based third-party data: Collected with clear consent
These insights help marketers identify high-intent prospects while maintaining transparency and trust.
Best Practices for Using Ethical Intent Data
• Be transparent about data collection and usage
• Prioritize user consent and control
• Focus on first-party and contextual data sources
• Align sales and marketing teams around intent insights
• Regularly review compliance and data governance policies
Challenges Businesses Should Consider
While ethical intent data offers major benefits, organizations may face challenges such as:
• Reduced reliance on large-scale third-party datasets
• The need for better first-party data strategies
• Balancing personalization with privacy expectations
However, these challenges are part of building a more sustainable marketing approach.
Conclusion
Ethical intent data is more than just a trend it’s the future of responsible B2B marketing. As buyers demand greater transparency and privacy standards continue to evolve, businesses must adopt smarter and more trustworthy ways to understand customer intent.
The brands making the shift today are not only protecting themselves for the future they’re building stronger relationships based on trust, relevance, and respect.
In the new era of B2B marketing, success will belong to companies that can balance data intelligence with ethical responsibility.
INTENT AMPLIFY is evolving fast. Are you keeping up? Read more at intentamplify.com
To participate in our interviews, please write to our Media Room at info@intentamplify.com
B2B marketing is entering a new era one where privacy, transparency, and trust matter just as much as targeting and personalization. For years, marketers relied heavily on third-party tracking and aggressive data collection to understand buyer behavior. But today, that approach is rapidly losing effectiveness.
As privacy regulations tighten and buyers become more aware of how their data is used, businesses are turning to a more responsible approach: ethical intent data.
What Is Ethical Intent Data?
Ethical intent data refers to buyer behavior insights collected transparently, responsibly, and with user consent. It helps marketers understand what prospects are researching and when they may be ready to buy without violating privacy expectations.
Unlike traditional intent data practices, ethical intent data focuses on:
• Consent-based data collection
• Transparency in how data is used
• Compliance with privacy regulations
• Respect for user trust and control
In simple terms, it’s about gathering valuable insights while putting privacy and ethics first.
Why Traditional Intent Data Is Losing Relevance
Traditional intent data models often relied on third-party cookies and unclear tracking methods. But several major changes are reshaping the landscape:
• Browsers are phasing out third-party cookies
• Privacy laws are becoming stricter worldwide
• Buyers are demanding greater transparency
• Companies face increasing compliance risks
As a result, many older tracking methods are becoming less reliable and more difficult to justify.
Why Top B2B Brands Are Switching to Ethical Intent Data
1. Building Trust with Buyers
Trust is now a competitive advantage. Brands that respect privacy and communicate transparently are more likely to earn long-term customer loyalty.
2. Staying Compliant with Privacy Regulations
Ethical intent data helps companies align with evolving privacy laws and avoid legal or reputational risks.
3. Improving Data Accuracy
Consent-driven and first-party data sources are often more reliable because they come directly from engaged users.
4. Preparing for a Cookie-Free Future
As third-party cookies disappear, ethical data strategies offer a sustainable and future-ready alternative.
5. Delivering Smarter Personalization
Ethical intent data still allows for relevant targeting and personalization without intrusive tracking methods.
How Ethical Intent Data Works
Ethical intent data typically combines:
• First-party data: Website visits, CRM insights, email engagement
• Contextual signals: Content topics and research behavior
• Permission-based third-party data: Collected with clear consent
These insights help marketers identify high-intent prospects while maintaining transparency and trust.
Best Practices for Using Ethical Intent Data
• Be transparent about data collection and usage
• Prioritize user consent and control
• Focus on first-party and contextual data sources
• Align sales and marketing teams around intent insights
• Regularly review compliance and data governance policies
Challenges Businesses Should Consider
While ethical intent data offers major benefits, organizations may face challenges such as:
• Reduced reliance on large-scale third-party datasets
• The need for better first-party data strategies
• Balancing personalization with privacy expectations
However, these challenges are part of building a more sustainable marketing approach.
Conclusion
Ethical intent data is more than just a trend it’s the future of responsible B2B marketing. As buyers demand greater transparency and privacy standards continue to evolve, businesses must adopt smarter and more trustworthy ways to understand customer intent.
The brands making the shift today are not only protecting themselves for the future they’re building stronger relationships based on trust, relevance, and respect.
In the new era of B2B marketing, success will belong to companies that can balance data intelligence with ethical responsibility.
INTENT AMPLIFY is evolving fast. Are you keeping up? Read more at intentamplify.com
To participate in our interviews, please write to our Media Room at info@intentamplify.com
Privacy Meets Precision: The Rise of Ethical Intent Data in B2B Marketing
B2B marketing is entering a new era one where privacy, transparency, and trust matter just as much as targeting and personalization. For years, marketers relied heavily on third-party tracking and aggressive data collection to understand buyer behavior. But today, that approach is rapidly losing effectiveness.
As privacy regulations tighten and buyers become more aware of how their data is used, businesses are turning to a more responsible approach: ethical intent data.
What Is Ethical Intent Data?
Ethical intent data refers to buyer behavior insights collected transparently, responsibly, and with user consent. It helps marketers understand what prospects are researching and when they may be ready to buy without violating privacy expectations.
Unlike traditional intent data practices, ethical intent data focuses on:
• Consent-based data collection
• Transparency in how data is used
• Compliance with privacy regulations
• Respect for user trust and control
In simple terms, it’s about gathering valuable insights while putting privacy and ethics first.
Why Traditional Intent Data Is Losing Relevance
Traditional intent data models often relied on third-party cookies and unclear tracking methods. But several major changes are reshaping the landscape:
• Browsers are phasing out third-party cookies
• Privacy laws are becoming stricter worldwide
• Buyers are demanding greater transparency
• Companies face increasing compliance risks
As a result, many older tracking methods are becoming less reliable and more difficult to justify.
Why Top B2B Brands Are Switching to Ethical Intent Data
1. Building Trust with Buyers
Trust is now a competitive advantage. Brands that respect privacy and communicate transparently are more likely to earn long-term customer loyalty.
2. Staying Compliant with Privacy Regulations
Ethical intent data helps companies align with evolving privacy laws and avoid legal or reputational risks.
3. Improving Data Accuracy
Consent-driven and first-party data sources are often more reliable because they come directly from engaged users.
4. Preparing for a Cookie-Free Future
As third-party cookies disappear, ethical data strategies offer a sustainable and future-ready alternative.
5. Delivering Smarter Personalization
Ethical intent data still allows for relevant targeting and personalization without intrusive tracking methods.
How Ethical Intent Data Works
Ethical intent data typically combines:
• First-party data: Website visits, CRM insights, email engagement
• Contextual signals: Content topics and research behavior
• Permission-based third-party data: Collected with clear consent
These insights help marketers identify high-intent prospects while maintaining transparency and trust.
Best Practices for Using Ethical Intent Data
• Be transparent about data collection and usage
• Prioritize user consent and control
• Focus on first-party and contextual data sources
• Align sales and marketing teams around intent insights
• Regularly review compliance and data governance policies
Challenges Businesses Should Consider
While ethical intent data offers major benefits, organizations may face challenges such as:
• Reduced reliance on large-scale third-party datasets
• The need for better first-party data strategies
• Balancing personalization with privacy expectations
However, these challenges are part of building a more sustainable marketing approach.
Conclusion
Ethical intent data is more than just a trend it’s the future of responsible B2B marketing. As buyers demand greater transparency and privacy standards continue to evolve, businesses must adopt smarter and more trustworthy ways to understand customer intent.
The brands making the shift today are not only protecting themselves for the future they’re building stronger relationships based on trust, relevance, and respect.
In the new era of B2B marketing, success will belong to companies that can balance data intelligence with ethical responsibility.
INTENT AMPLIFY is evolving fast. Are you keeping up? Read more at intentamplify.com
To participate in our interviews, please write to our Media Room at info@intentamplify.com
0 Comments
0 Shares