Digital Threat Intelligence Management Market Growth, Share, and Trends
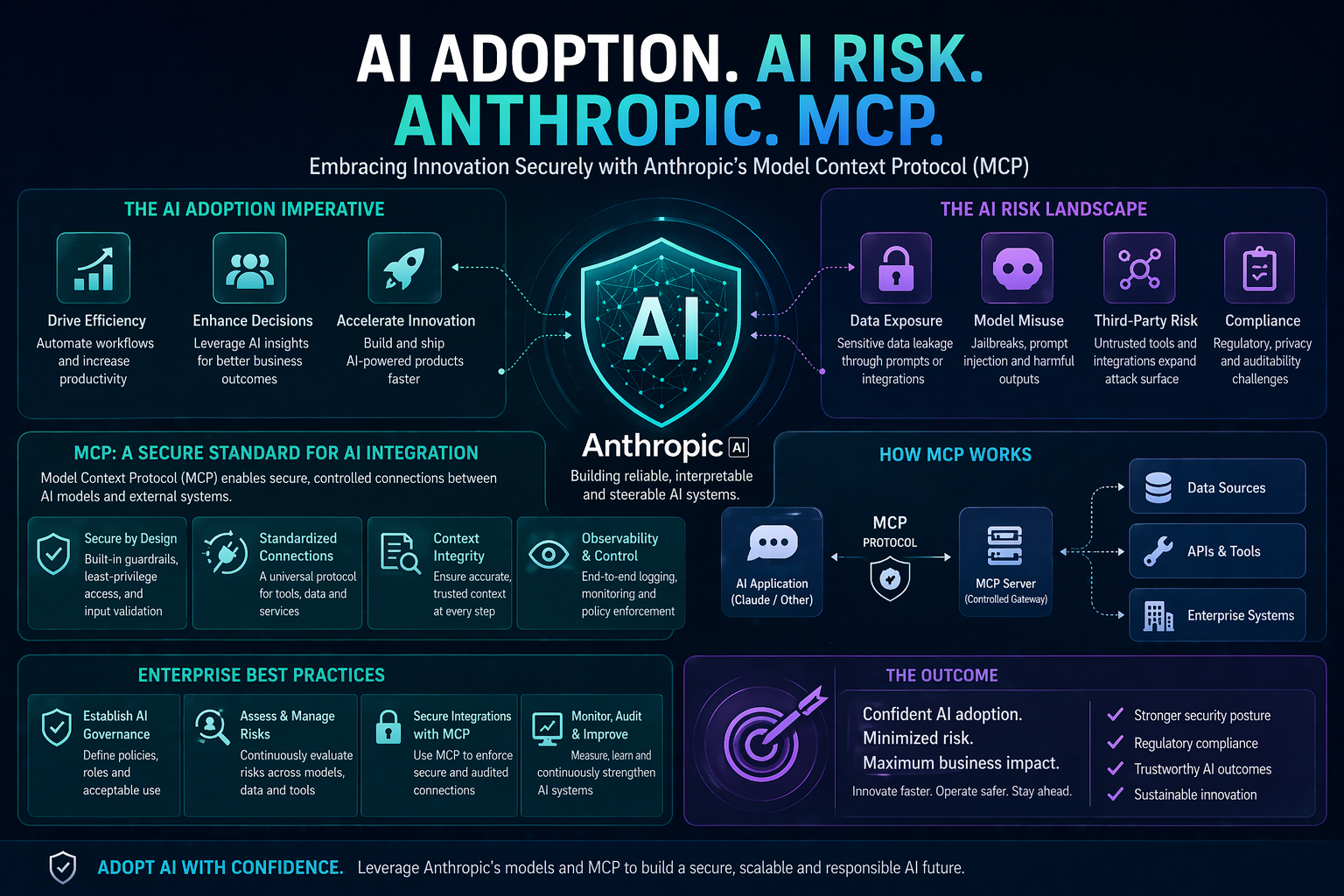
In today’s digital age, organizations face an ever-evolving cyber threat landscape. Cybercriminals are growing more sophisticated, employing advanced tactics to exploit vulnerabilities in networks, applications, and data systems. Traditional security measures, such as firewalls and antivirus software, are no longer sufficient to counter these dynamic threats. This is where Digital Threat Intelligence Management (DTIM) becomes a critical component of an organization’s cybersecurity strategy.
Click Here For More:
https://qksgroup.com/market-research/market-share-digital-threat-intelligence-management-dtim-2025-worldwide-2386
DTIM equips organizations with actionable intelligence that helps anticipate and mitigate cyber threats before they can cause significant damage. By analyzing patterns in cyber attacks, understanding threat actors’ motives, and monitoring emerging vulnerabilities, DTIM allows security teams to stay one step ahead of potential attackers. Organizations can proactively identify weaknesses in their systems and implement targeted measures to reduce risk, rather than reacting only after a breach has occurred.
One of the key advantages of DTIM is its ability to enhance incident response. When a security event occurs, timely and accurate threat intelligence enables teams to quickly understand the nature of the attack, assess its impact, and implement appropriate containment and remediation strategies. This reduces downtime, limits financial and reputational damage, and strengthens overall resilience against cyber threats.
Additionally, DTIM plays a vital role in ensuring regulatory compliance. Many industries are subject to stringent data protection and cybersecurity regulations. Implementing comprehensive threat intelligence management ensures that organizations maintain visibility over potential risks and can demonstrate due diligence in protecting sensitive information. This not only safeguards critical assets but also fosters trust with clients, partners, and stakeholders.
As cyber threats continue to evolve, organizations cannot afford to rely solely on reactive security measures. Comprehensive DTIM solutions provide a strategic approach to cybersecurity, combining advanced analytics, threat monitoring, and actionable insights to safeguard digital assets. By integrating DTIM into their cybersecurity framework, organizations can anticipate attacks, respond efficiently, and maintain robust defenses in an increasingly complex digital environment.
In conclusion, Digital Threat Intelligence Management is no longer optional—it is essential for organizations aiming to maintain operational continuity, protect sensitive data, and stay ahead of cyber adversaries. Investing in DTIM not only enhances security posture but also ensures that organizations are well-prepared to face the future of cybersecurity threats.
Key questions this study will answer:
At what pace is the Digital Threat Intelligence Management (DTIM) market growing?
What are the key market accelerators and market restraints impacting the global Digital Threat Intelligence Management (DTIM) market?
Which industries offer maximum growth opportunities during the forecast period?
Which global region expects maximum growth opportunities in the Digital Threat Intelligence Management (DTIM) market?
Which customer segments have the maximum growth potential for the Digital Threat Intelligence Management (DTIM) solution?
Which deployment options of Digital Threat Intelligence Management (DTIM) solutions are expected to grow faster in the next 5 years?
Market Forecast Digital Threat Intelligence Management (DTIM):
https://qksgroup.com/market-research/market-forecast-digital-threat-intelligence-management-dtim-2026-2030-worldwide-2190
Strategic Market Direction:
The strategic market direction for Digital Threat Intelligence Management is focused on enhancing integration, predictive capabilities, and user accessibility. Vendors are increasingly adopting AI and machine learning to enable predictive analytics that can foresee and mitigate potential threats before they materialize. There is also a significant push towards integrating DTIM solutions with broader cybersecurity ecosystems, including SIEM, SOAR (Security Orchestration, Automation, and Response), and other security tools, to provide a unified and efficient approach to threat management. Additionally, the market is moving towards more user-friendly interfaces and dashboards that make it easier for security teams to interpret and act on threat intelligence data. This direction aims to create more intelligent, integrated, and accessible DTIM solutions that can effectively protect organizations in a rapidly evolving cyber threat landscape.
Vendors Covered:
Rapid7, Kaspersky, Recorded Future, Microsoft, Cybersixgill, ThreatBook, ThreatConnect, ThreatQ, ZeroFox, Intel471, Anomali, Threater, Outpost24, Centripetal, Crowdstrike, Cyberint, Cyware, ReliaQuest, EclecticIQ, Trellix, Flashpoint, Group-IB, Security Scorecard, Mandiant.
#DigitalThreatIntelligenceManagement #DTIM #Cybersecurity #CyberThreats #ThreatDetection #RiskManagement #ThreatIntelligence #Security #ITSecurity #CyberDefense #Security #DigitalThreatIntelligenceManagementMarket #ThreatIntelligenceManagementMarket #ThreatIntelligenceManagement #ManagedThreatIntelligence #DTIMMarket Digital Threat Intelligence Management Market Growth, Share, and Trends
In today’s digital age, organizations face an ever-evolving cyber threat landscape. Cybercriminals are growing more sophisticated, employing advanced tactics to exploit vulnerabilities in networks, applications, and data systems. Traditional security measures, such as firewalls and antivirus software, are no longer sufficient to counter these dynamic threats. This is where Digital Threat Intelligence Management (DTIM) becomes a critical component of an organization’s cybersecurity strategy.
Click Here For More: https://qksgroup.com/market-research/market-share-digital-threat-intelligence-management-dtim-2025-worldwide-2386
DTIM equips organizations with actionable intelligence that helps anticipate and mitigate cyber threats before they can cause significant damage. By analyzing patterns in cyber attacks, understanding threat actors’ motives, and monitoring emerging vulnerabilities, DTIM allows security teams to stay one step ahead of potential attackers. Organizations can proactively identify weaknesses in their systems and implement targeted measures to reduce risk, rather than reacting only after a breach has occurred.
One of the key advantages of DTIM is its ability to enhance incident response. When a security event occurs, timely and accurate threat intelligence enables teams to quickly understand the nature of the attack, assess its impact, and implement appropriate containment and remediation strategies. This reduces downtime, limits financial and reputational damage, and strengthens overall resilience against cyber threats.
Additionally, DTIM plays a vital role in ensuring regulatory compliance. Many industries are subject to stringent data protection and cybersecurity regulations. Implementing comprehensive threat intelligence management ensures that organizations maintain visibility over potential risks and can demonstrate due diligence in protecting sensitive information. This not only safeguards critical assets but also fosters trust with clients, partners, and stakeholders.
As cyber threats continue to evolve, organizations cannot afford to rely solely on reactive security measures. Comprehensive DTIM solutions provide a strategic approach to cybersecurity, combining advanced analytics, threat monitoring, and actionable insights to safeguard digital assets. By integrating DTIM into their cybersecurity framework, organizations can anticipate attacks, respond efficiently, and maintain robust defenses in an increasingly complex digital environment.
In conclusion, Digital Threat Intelligence Management is no longer optional—it is essential for organizations aiming to maintain operational continuity, protect sensitive data, and stay ahead of cyber adversaries. Investing in DTIM not only enhances security posture but also ensures that organizations are well-prepared to face the future of cybersecurity threats.
Key questions this study will answer:
At what pace is the Digital Threat Intelligence Management (DTIM) market growing?
What are the key market accelerators and market restraints impacting the global Digital Threat Intelligence Management (DTIM) market?
Which industries offer maximum growth opportunities during the forecast period?
Which global region expects maximum growth opportunities in the Digital Threat Intelligence Management (DTIM) market?
Which customer segments have the maximum growth potential for the Digital Threat Intelligence Management (DTIM) solution?
Which deployment options of Digital Threat Intelligence Management (DTIM) solutions are expected to grow faster in the next 5 years?
Market Forecast Digital Threat Intelligence Management (DTIM): https://qksgroup.com/market-research/market-forecast-digital-threat-intelligence-management-dtim-2026-2030-worldwide-2190
Strategic Market Direction:
The strategic market direction for Digital Threat Intelligence Management is focused on enhancing integration, predictive capabilities, and user accessibility. Vendors are increasingly adopting AI and machine learning to enable predictive analytics that can foresee and mitigate potential threats before they materialize. There is also a significant push towards integrating DTIM solutions with broader cybersecurity ecosystems, including SIEM, SOAR (Security Orchestration, Automation, and Response), and other security tools, to provide a unified and efficient approach to threat management. Additionally, the market is moving towards more user-friendly interfaces and dashboards that make it easier for security teams to interpret and act on threat intelligence data. This direction aims to create more intelligent, integrated, and accessible DTIM solutions that can effectively protect organizations in a rapidly evolving cyber threat landscape.
Vendors Covered:
Rapid7, Kaspersky, Recorded Future, Microsoft, Cybersixgill, ThreatBook, ThreatConnect, ThreatQ, ZeroFox, Intel471, Anomali, Threater, Outpost24, Centripetal, Crowdstrike, Cyberint, Cyware, ReliaQuest, EclecticIQ, Trellix, Flashpoint, Group-IB, Security Scorecard, Mandiant.
#DigitalThreatIntelligenceManagement #DTIM #Cybersecurity #CyberThreats #ThreatDetection #RiskManagement #ThreatIntelligence #Security #ITSecurity #CyberDefense #Security #DigitalThreatIntelligenceManagementMarket #ThreatIntelligenceManagementMarket #ThreatIntelligenceManagement #ManagedThreatIntelligence #DTIMMarket